Voltage and reset glitch attacks are a class of physical fault injection techniques in which an attacker briefly disturbs a device power or reset signals, causing the central processing unit or system on chip to enter an unintended or undefined state during execution. Such transient faults can result in skipped instructions, data corruption, altered control flow, or the circumvention of critical security checks, potentially enabling privilege escalation or arbitrary code execution.
Research into power manipulation as a means of inducing hardware faults has been ongoing since the 1990s, with early demonstrations targeting smartcards. Although modern manufacturers have introduced countermeasures by reinforcing power and reset domains, this report demonstrates that many designs still lack sufficient hardware level protections, leaving systems vulnerable to voltage fault injection attacks.
Xbox 360
Anyone who used to play XB360 would have at one point come across someone who had exploited their console and was running unsigned code. The original attacks on the XB360 abused the GPU’s JTAG port to run a version of the King Kong Exploit.
However, starting from dashboard version 2.0.7371 Microsoft patched the vulnerability and also burnt efuses preventing users from downgrading their console to a vulnerable version.
Microsoft later patched the exploit with hardware revisions (S/E motherboards), preventing users from exploiting their consoles even if another software exploit was found.
A new method was required to exploit the console…
Xbox 360 RGH
In August 2011, GliGli release an exploit known as the Reset Glitch Hack, a hardware exploit that allows for unsigned code to be ran once again. What makes this attach different is that unlike it’s predecessor the JTAG attack, RGH is unpatchable in software. This is a true hardware exploit which cannot be rectified with an OTA update by Microsoft.
Under normal circumstances, a short pulse to the CPU_RESET pin on the Xbox’s CPU will reset the CPU completely. However, GliGli found that if the pulse is sent at just the right time (whilst a specific instruction is being processed) the CPU won’t restart like expected but rather skip over a critical instruction which means you bypass the hash comparison module.
Due to the CPU clock speed being so high, the timing accuracy of this short pulse is critical. In order to have the highest chance of success, the clock speed is slowed down by utilising the CPU_PLL_BYPASS pin. By enabling this pin, the multiplication of the internal clock that is usually applied byt the Phase-Lock Loop (PLL) is bypassed, leaving the CPU running at a much slower speed (128 times slower in this case).
The process is as follows:
1. Snoop on the POST signals from the Xbox to keep track of how far through the boot process it is.
2. Latch the CPU_PLL_BYPASS just before CB is about to validate CD’s hashes to slow down the CPU to roughly 25 MHz.
3. Latch the CPU_RESET line for (4-60ns) when CB is in the middle of the secure_memcmp function.
4. Stop latching the CPU_PLL_BYPASS and allow the CPU to go back to normal clock speed and allow a custom payload to be run.
This process only works if the CPU is currently executing a mr (move register) instruction, if the glitch occurs during this execution, the destination value will be assigned as zero instead of the source register.
This then allows the CPU to bypass checks related to the hash comparisons of the bootloader, allowing the user to make changes that would normally be prevented.

NINTENDO SWITCH
Skip forward to the year 2017 and the Nintendo switch is released. There were several software bugs found in the original firmware (quickly patched by Nintendo) that allowed for exploitation.
There was a very famous hack called the RCM exploit which plagued Nintendo’s first hardware revision, a memory buffer overflow paired with the RCM pre-boot mode in the Nvidia Tegra x1 chips allowed for unsigned code to be executed. This mistake was costly for Nintendo as the vulnerability was burnt directly onto the BootROM, the only fix was a hardware revision.
NINTENDO SWITCH RGH
Just like with the Xbox 360, the answer to exploiting the revised Switch was a voltage glitch attack.
This time I wanted to take a practical look at how these voltage glitch attacks were being performed on the devices.
The method of injecting a voltage glitch can differ depending on the device under test. Simple device with no voltage regulators on board can simply be glitched by modifying the external power supply (for example using a programmable power supply).
In the case of the Nintendo Switch, there are many voltage regulators built on the PCB to feed different parts of the board.
CROWBAR circuit
The crowbar circuit was originally designed for preventing an overvoltage or surge condition, protecting sensitive electronics that could be damaged in such conditions. The idea of the circuit is to force a rapid short circuit between the voltage line and ground. causing a voltage drop.
Typically, the circuit is made up of MOSFET and is placed between the supply voltage of the device (in this case the Tegra X1 chip) and GND.
In the case of the Nintendo Switch, the hardware designers placed decoupling capacitors across the power rails of the Tegra X1 chip, these help reduce noise and stabilise the power going into the chip. Ironically, these can be used as a good point to solder to (although it can be better to remove them entirely for the attack as they will reduce the effect of the crowbar circuit).

Figure taken from The Forgotten Threat of Voltage Glitching: A Case Study on Nvidia Tegra X2 SoCs
The Attack
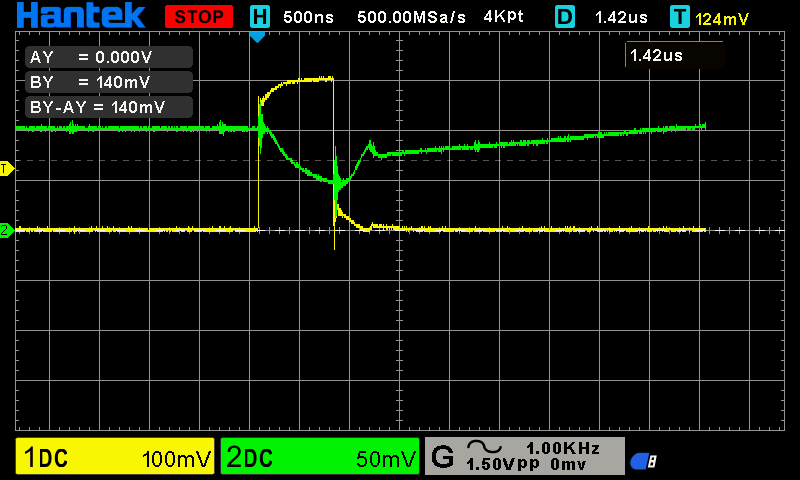
The image on right is a screen grab from my oscilloscope showing the glitch in action.
Channel 1 (yellow) is the MOSFET’s Gate voltage
Channel 2 (Green) is the MOSFET’s drain voltage
Channel 2 shows the drop in voltage during the roughly 750ns glitch period.